I was recently asked to contribute my thoughts on how election monitors using simple mobile phones could improve their safety and security when working in hostile environments. More specifically, the goal was to find techniques by which their use of SMS messaging to report back to a centralized service or team could be done in a more secure, private manner, that would make it more difficult for an adversary working against them to stop, block or track. All of this must be done without software or special hardware, instead just relying on easily teachable techniques.
Here’s the collection of tips and ideas I came up with on short notice. It is by no means complete, but I felt it would be useful to publish these to a wider audience here on my blog. Finally, before you say “well couldn’t criminals and terrorists use these techniques too?”, I will refer you to an excellent Abuse FAQ page from the Tor Project which covers this very topic (“Criminals can already do bad things. Since they’re willing to break laws, they already have lots of options available that provide better privacy than Tor provides”).
Now, on to the topic at hand…
Changing Your SIM Card
Often the first thing that comes to mind when people think about reducing tracking of their mobile phone is to change their SIM card. Unfortunately, changing SIM cards isn’t a reliable solution to stop centralized tracking because each phone also has an IMEI (http://en.wikipedia.org/wiki/International_Mobile_Equipment_Identity) that uniquely identifies the underlying phone hardware itself. This means that even if you change your SIM card, the phone’s unique identifier can still be tracked. Still a new SIM card would change the phone number that is displayed or logged on the receivers phone, which could buy someone time or throw off a lazy investigator.
You can check your IMEI by typing in: *#06# or something similar depending upon carrier or phone. There are a number of cheap Chinese phones on the market in some countries that have an IMEI of 000000000000, which can come in handy if they are those types of things available. It is illegal in most countries to change the IMEI or to use a phone with an invalid IMEI.
Airplane Mode Ain’t Just for Airplanes
If their phone has “Airplane Mode” or a way to disconnect from a network or manually choose a network, that usually works as well as taking the battery out. This is useful if they still want to take pictures, notes, record message, queue up SMS messages to be sent once they reconnect in a different location from where the data was captured.
To step back a bit, it is important to understand, that mobile phones are always in constant contact with the cellular towers in the area. As you move about, your phone is in constant negotiation with different towers to connect to the best single, check for incoming calls, SMS message and so on. In addition, the server provider is checking your identifiers to make sure your phone is valid to work on the network, that you have an activated account, that your hardware isn’t blacklisted (aka stolen, etc), and so on. In summary, even if you aren’t using your phone, your phone is being tracked for operational and billing purposes, not necessarily malicious. However, it must be understand that this same data can be used by authorities for whatever purpose they like and is legal in the current country or context.
In theory, if you put your phone into “Airplane Mode” all signals emanating from your phone are stopped.
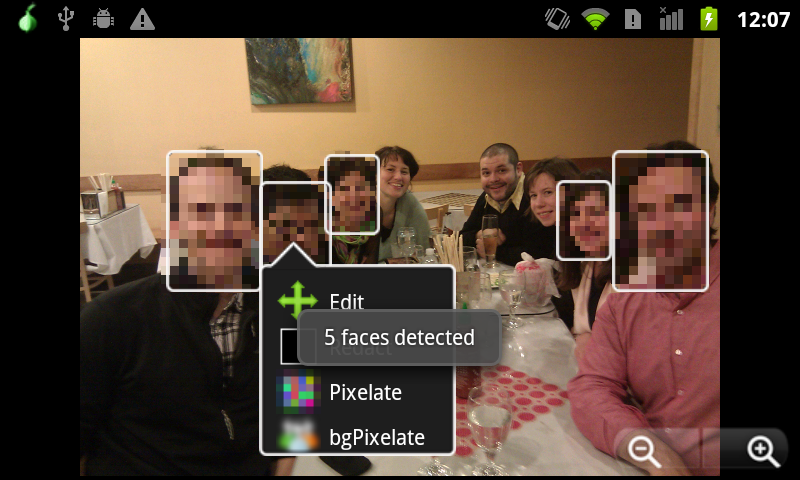
Complicating Monitoring by Turning Text into Pictures
If picture messages or MMS is available, write a message/code on paper and take a picture of it instead of sending it as text. Harder to automatically filter/monitor, and that the small resolution on the screen harder to read… if they can get the message on a PC on the receiving end, it can be zoomed up, but if the sender is stopped by local authorities, they may not see it.
In addition, picture messages of colors can also be a code:
- Blue Sky = “okay”
- Red Sign = “problem”
- Brown Dirt = “Ballot Stuffing”
Your Very Own Secret Code
Come with a very basic text code that say involves ten digits, with each different representing 0-9 of possible states.
- 0-9: how long is the wait (in hours)
- 0-9: how bad is intimidation from militia (scale)
- 0-9: how good is the turnout (scale)
- 0-9: general code (0 = no problems, 1 = polling place closed, 2 = armed men outside, 3 = riot, 4 = no ballots available)
could then result in a code:
- 2190 <— this would be a pretty good polling place
- 9912 <—- this would be a report of trouble
You could easily write this on piece of paper and take a picture of it as well.
Again, this type of code would just look like gibberish at the local level, and perhaps buy some time at a state surveillance level until they got their own copy of the code. At the least you would be making them work some more to figure it out, and make them less able to filter by keywords.
Mobile Pyramid Scheme aka Improved Autonomy
Local groups can send to one local person, and then that person can forward each message to another level up the tree and so on. This would enable a bit more protection than all field election monitors texting to a centralized number. It introduces some other issues around reliability of the data and complexity of the process, but in exchange you help foster autonomy and decentralization, two great tools to improve safety and privacy in your overall network.
Managing What Gets Logged
By default, phones tend to log and track everything you do, in the name of convenience. This includes all the text messages you send. The problem is that if a person is detained, it can be difficult to quickly delete those messages before the detainers take away the phone to see what they can learn from it.
Most phones offer a way to NOT save outgoing SMS messages and also to potentially delete inbound after they are read. This feature should be utilized. In addition, numbers should be memorized and manually entered, instead of stored in an address book.
More Ideas?
If you are reading this post and have your own thoughts or firsthand experience to contribute to the discussion, please add them using the comment section below. I will make sure the right people see this information. Your insight and creativity can make a difference!