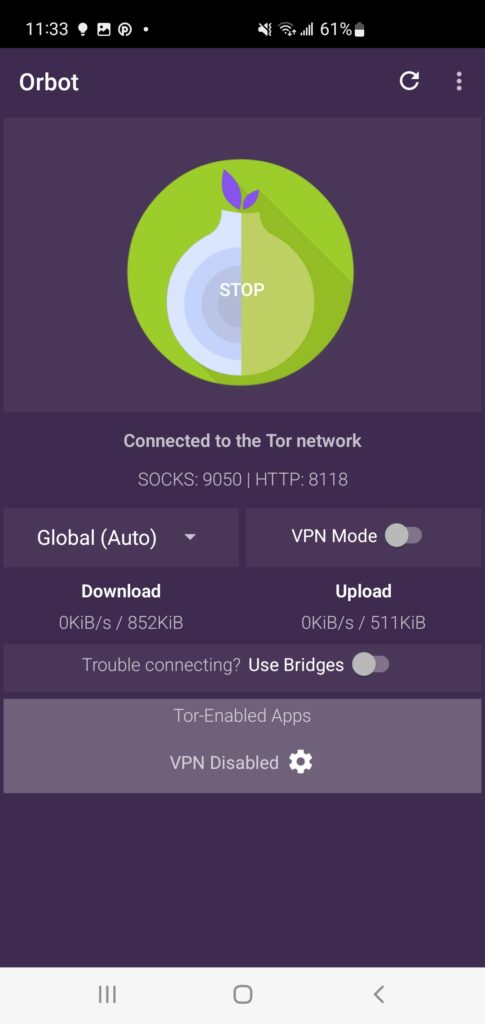
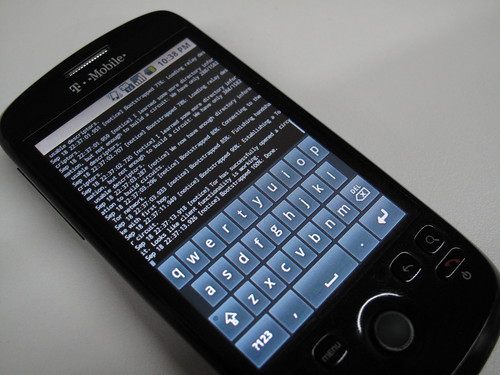
I’d like to make this post without much fanfare. Just looking to share information on the work I’ve been doing with the fantastically radical team over at the Tor Project, as part of my work on the Guardian Project. We have successfully ported the native C Tor app to Android and built an Android application bundle that installs, runs and provides the glue needed to make it useful to end users…. secure, anonymous access to the web via Tor on Android is now a reality. (Update: Tor doesn’t magically encrypt all of your Internet activities, though. You should understand what Tor does and does not do for you.)
However, there is still much work to be done… read on!
1) Tor 0.2.2.5-alpha release contains all the necessary code for building the Tor binary exe using the Android C SDK. I utilized http://github.com/tmurakam/droid-wrapper toolchain wrapper scripts to make life easier. This will produce the output Tor exe that can run on Android w/o needing root.
Update: Thanks to Jake, you can now read the updated Orbot BUILD doc for the step by step build how to.
(thanks to ioerror for the pic)
At this point, we are pretty convinced that the performance and efficiency of the C binary is quite significantly better than the Java-based ports of Tor running within Dalvik… this translate to a better experience for the user, with no noticeable increase in battery drain or lag on the rest of the device while Tor is running in the background.
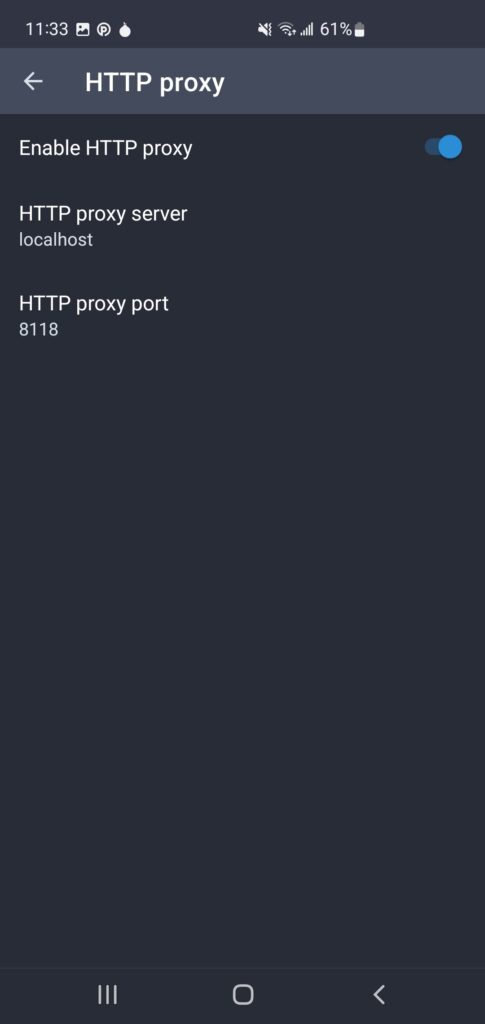
2) Orbot – this is the new Android app which bundles the Tor binary, handles its proper installation on the device and then provides a gui for starting/stopping, view the log and torrc, etc. It also provides a built-in HTTP Proxy and is licensed under the Tor license.



Just to be clear – we aren’t using the NDK or a shared library… we are actually extracting a binary and managing it via Runtime.getRuntime().exec() calls. This is 100% supported – who knew?! More info on how to do this here
The first code is up here… all is working, but def needs much polish:
https://svn.torproject.org/svn/projects/android/trunk/Orbot/
This post is in part a call for developers to contribute to the continued development of Orbot, so we can get it to a 1.0 state. The other big task is to modify the open-source, privacy focused Shadow browser, from the University of Cambridge DTG group, in order to make it work with our HTTP proxy. That would be a really great step forward, as right now, we have to ask users to set their global APN (read: https://svn.torproject.org/svn/projects/android/trunk/Orbot/INSTALL)
Thanks for everyone’s help and support to get here. I’d like to keep pushing on to a public release via the App Market very soon. Let me know if you’d like to contribute in any way – code, screen designs, icons, testing….
Domo arigato, Mr. Orbot-o!!